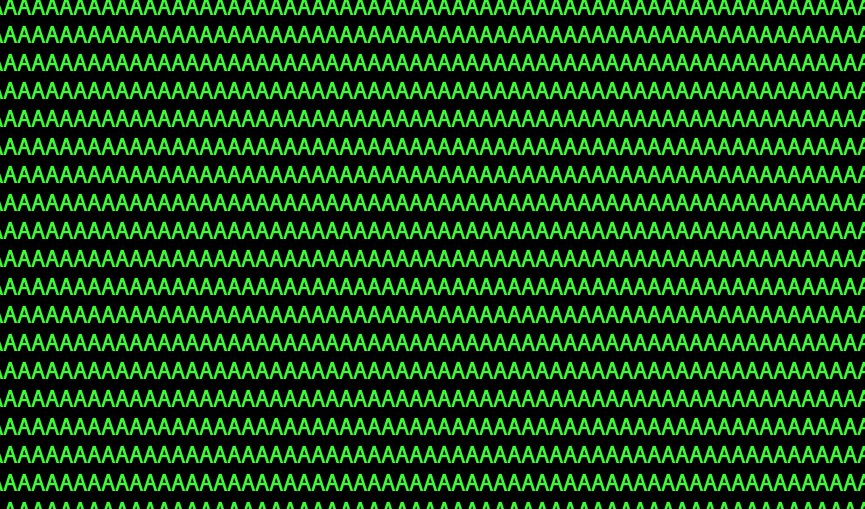
 hugow
hugow 
 137
137
Position
 11800
11800
Points
 323
323
Challenges
 26
26
Compromissions
70%
App - Script
660 Points23 / 33
- o Bash - System 1
- o sudo - weak configuration
- o Bash - System 2
- x LaTeX - Input
- o Powershell - Command Injection
- x AppArmor - Jail Introduction
- o Bash - unquoted expression injection
- x Docker - I am groot
- o Perl - Command injection
- o Powershell - SecureString
- o Bash - cron
- x LaTeX - Command execution
- o Python - input()
- x R : Code Execution
- o Powershell - Basic jail
- o Python - pickle
- o Bash - quoted expression injection
- x Docker - Sys-Admin’s Docker
- o Shared Objects hijacking
- o SSH - Agent Hijacking
- x AppArmor - Jail Medium
- o Bash - race condition
- x Docker - Talk through me
- o Python - format string
- o Python - PyJail 1
- o PHP - Jail
- o Python - PyJail 2
- o Python - Jail - Exec
- o Javascript - Jail
- o Python - Jail - Garbage collector
- o Bash - Restricted shells
- x Python - Eval Is Evil
- x Deep learning - Malicious model
44%
App - System
2445 Points41 / 93
- o ELF x86 - Stack buffer overflow basic 1
- x ELF x64 - Basic heap overflow
- o ELF x86 - Stack buffer overflow basic 2
- o PE32 - Stack buffer overflow basic
- o ELF x86 - Format string bug basic 1
- o ELF x64 - Stack buffer overflow - basic
- o ELF x86 - Format string bug basic 2
- o ELF x86 - Race condition
- o ELF ARM - Stack buffer overflow - basic
- o ELF MIPS - Stack buffer overflow - No NX
- x ELF x64 - Double free
- o ELF x86 - Stack buffer overflow basic 3
- o ELF x86 - Use After Free - basic
- x ELF ARM - Stack Spraying
- x ELF x64 - Stack buffer overflow - PIE
- o ELF x86 - BSS buffer overflow
- o ELF x86 - Stack buffer overflow basic 4
- o ELF x86 - Stack buffer overflow basic 6
- o ELF x86 - Format String Bug Basic 3
- x PE32 - Advanced stack buffer overflow
- o ELF ARM - Basic ROP
- x ELF MIPS - Basic ROP
- x ELF RISC-V - Intro - let’s do the ROP
- x ELF x64 - Stack buffer overflow - Stack pivot
- o ELF x86 - Stack buffer overflow - C++ vtables
- x PE32+ Format string bug
- o ELF x64 - Logic bug
- x ELF x86 - Bug Hunting - Several issues
- o ELF x86 - Stack buffer and integer overflow
- o ELF x86 - Stack buffer overflow - ret2dl_resolve
- o ELF x86 - Stack buffer overflow basic 5
- o ELF x64 - Stack buffer overflow - advanced
- x ELF MIPS - Format String Glitch
- x ELF x64 - Heap Filling
- o ELF x86 - Information leakage with Stack Smashing Protector
- x ELF x64 - File Structure Hacking
- x ELF ARM - Race condition
- o ELF x64 - Browser exploit - Intro
- x ELF x64 - Buggy VM
- x ELF x64 - Heap Safe-Linking Bypass
- x ELF x64 - ret2dl_init
- o ELF x86 - Out of bounds attack - French Paradox
- x ELF x86 - Remote BSS buffer overflow
- o ELF x86 - Remote Format String bug
- x PE32+ Basic ROP
- o ELF x64 - Remote heap buffer overflow - tcache
- o ELF x86 - Blind remote format string bug
- x LinKern ARM - vulnerable syscall
- o LinKern x86 - Buffer overflow basic 1
- x ELF x64 - Sigreturn Oriented Programming
- o LinKern x86 - Null pointer dereference
- x ELF x64 - Syscall chaining
- o LinKern x64 - Race condition
- x ELF ARM - Alphanumeric shellcode
- x ELF MIPS - URLEncoded Format String bug
- x ELF x64 - Blind SROP
- x ELF x64 - Heap Hop
- o ELF x86 - Hardened binary 1
- o ELF x86 - Hardened binary 2
- o ELF x86 - Hardened binary 3
- o ELF x86 - Hardened binary 4
- x LinKern MIPSel - Vulnerable ioctl
- x LinKern x64 - reentrant code
- x ELF ARM - Heap format string bug
- x ELF ARM - Format String bug
- x ELF ARM - Use After Free
- x ELF x64 - FILE structure hijacking
- x ELF x64 - Heap feng-shui
- o ELF x64 - Off-by-one bug
- o ELF x86 - Hardened binary 5
- x LinKern ARM - Stack Overflow
- x LinKern x86 - basic ROP
- x ELF ARM - Heap Off-by-One
- x ELF x64 - Advanced blind format string exploitation
- o ELF x64 - Remote Heap buffer overflow 1
- o ELF x86 - Hardened binary 6
- o ELF x86 - Hardened binary 7
- x ELF x86 - Remote stack buffer overflow - Hardened
- o LinKern x64 - RowHammer
- x LinKern x64 - SLUB off-by-one
- x ELF ARM - Heap buffer overflow - Wilderness
- x ELF ARM - Heap Overflow
- x ELF ARM64 - Heap Underflow
- x ELF x64 - Seccomp Whitelist
- x ELF x86 - Blind ROP
- x LinKern x64 - Memory exploration
- x WinKern x64 - Advanced stack buffer overflow - ROP
- x WinKern x64 - Use After Free
- x ELF x64 - Remote Heap buffer overflow 2
- x ELF x64 - Advanced Heap Exploitation - Heap Leakless & Fortified
- x ELF x64 - Blind ROP
- x ELF x64 - Browser exploit - BitString
- x ELF ARM64 - Multithreading
50%
Cracking
980 Points33 / 66
- o ELF x86 - 0 protection
- o ELF x86 - Basic
- o PE x86 - 0 protection
- o ELF C++ - 0 protection
- x Godot - 0 protection
- o PE DotNet - 0 protection
- x APK - Introduction
- o ELF MIPS - Basic Crackme
- o ELF x64 - Golang basic
- o ELF x86 - Fake Instructions
- o ELF x86 - Ptrace
- x Godot - Bytecode
- x WASM - Introduction
- x APK - Flutter Debug
- o ELF ARM - Basic Crackme
- x ELF x64 - Basic KeygenMe
- x Unity3D Save handling
- x Godot - Mono
- x PE DotNet - Basic Anti-Debug
- x PE DotNet - Basic Crackme
- o PYC - ByteCode
- o ELF x86 - No software breakpoints
- x Lua - Bytecode
- o MachO x64 - keygenme or not
- o ELF ARM - crackme 1337
- o ELF x86 - CrackPass
- o ELF x86 - ExploitMe
- o ELF x86 - Random Crackme
- o GB - Basic GameBoy crackme
- o PDF - Javascript
- o PE x86 - Xor Madness
- o Powershell DeObfuscation
- o ELF ARM - Crypted
- o ELF x64 - Crackme automating
- x Godot - 3D model
- x NRO ARM - Switch homebrew
- o PE x86 - SEHVEH
- o APK - Anti-debug
- o APK - Insomni’Droid
- x ELF x64 - Rust backdoor
- x ELF x64 - Rust Crackme
- x PE x64 - UEFI Secure Boot
- o APK - Root My Droid
- o ELF x64 - Nanomites - Introduction
- o ELF x86 - Anti-debug
- x PE DotNet - KeygenMe
- x PE x64 - Tables in shambles
- o PE x86 - AutoPE
- x PYC - Self Modifying (Byte)Code
- x PYC - Snakeygen
- o ELF x86 - KeygenMe
- x HackerMan
- x Unity - Mono - Basic Game Hacking
- x WASM - Find the NPC
- x Bash - VM
- x ELF x64 - KeyGenMe
- x ELF x64 - Anti-debug and equations
- x Unity - IL2CPP - Basic Game Hacking
- o ELF x64 - Nanomites
- o ELF x86 - Packed
- x PE x86 - RunPE
- x ELF x86 - VM
- x ELF x64 - Hidden Control Flow
- x Ringgit
- x Voracious Nanomites
- x White-Box Cryptography #2
56%
Cryptanalysis
1050 Points39 / 70
- o Encoding - ASCII
- o Encoding - UU
- x Hash - DCC
- x Hash - DCC2
- x Hash - LM
- o Hash - Message Digest 5
- x Hash - NT
- o Hash - SHA-2
- o Shift cipher
- x CISCO - Salted Password
- o Pixel Madness
- o ELF64 - PID encryption
- o File - PKZIP
- o Monoalphabetic substitution - Caesar
- x Circular Bit Shift
- o Known plaintext - XOR
- o Code - Pseudo Random Number Generator
- x Encoding - Codebook
- x File - PKZIP 2
- o File - Insecure storage 1
- o Polyalphabetic substitution - Vigenère
- o System - Android lock pattern
- o Transposition - Rail Fence
- o AES - CBC - Bit-Flipping Attack
- o AES - ECB
- x AES - ECB - Copy Paste
- o LFSR - Known plaintext
- o RSA - Factorisation
- o RSA - Decipher Oracle
- o Service - Timing attack
- o Monoalphabetic substitution - Polybe
- x Twisted secret
- o Initialisation Vector
- x Hill Cipher
- x GEDEFU
- x OTP - Implementation error
- o RSA - Corrupted key 1
- o RSA - Continued fractions
- o RSA - Common modulus
- o Service - Hash length extension attack
- x Shamir Secret Sharing - Introduction
- o AES - 4 Rounds
- o ECDSA - Introduction
- o RSA - Padding
- o RSA - Signature
- x Shamir Secret Sharing - Traitor
- o AES128 - CTR
- x PHP - mt_rand
- o Discrete logarithm problem
- o RSA - Corrupted key 2
- o RSA - Corrupted key 3
- o RSA - Multiple recipients
- x AES - Fault attack #1
- x FEAL - Differential Cryptanalysis
- x Enigma Machine
- x Side Channel - AES : CPA
- x ECDHE
- x RSA - H-rabin
- o RSA - Lee cooper
- o Service - CBC Padding
- x Side Channel - AES : first round
- x Polyalphabetic substitution - One Time Pad
- o White-Box Cryptography
- x AES - Weaker variant
- x Shamir Secret Sharing - Reduction
- x Hash - SHA-3
- x AES - Fault attack #2
- x Shamir Secret Sharing - Irreducible ?
- x AES-PMAC
- x ECDSA - Implementation error